Home / About
About Secutor
Who We Are
We’re an entrepreneurial enterprise born of a need in the marketplace: the need for affordable cybersecurity. We looked around the cybersecurity landscape and knew we could do better. We created an innovative business model that taps top-notch talent and protects your bottom line.
Today, Secutor is a team of over 100 Information Security and IT professionals with a wide variety of backgrounds. They’ve got a passion for identifying, containing and eradicating cybersecurity issues. And for serving you.
What We Do
We tackle cybersecurity challenges of virtually every size and any type. Our consultants have a wide range of specialties, including building enterprise-class vulnerability management programs, penetration testing for PCI compliance, network security architecture design, and managed SOC operation.
We also instill trust. As we see it, there is a firewall that actually needs to breached… the wall between you and your cybersecurity experts. We work hard to destroy that wall and keep it down, forever. In its place we form bonds based on transparency, value, and partnership.
Our Mission
Our mission is to deliver on-demand, affordable cybersecurity.
To put people first. To be your swift, expert and honest partners in cybersecurity.
Our Expertise
Application Security
Secutor’s consultants have in-depth experience across application development and application security. We understand the System Development Life Cycle (SDLC) and engineering processes that introduce vulnerabilities hackers exploit like SQL injection, XSS, and CSRF.
Cybersecurity
We understand a variety of information security disciplines including PCI, HIPAA, and GDPR compliance, risk management, network security and security architecture.
Security Architecture
Our team understands what it takes to be compliant with regulations like PCI DSS, HIPAA, GLBA, and GDPR like the back of their hand. We can write or revise security policies and standards and enhance data protection programs.
Threat & Vulnerability Management
Our experienced cybersecurity professionals are experts in Threat & Vulnerability Management including threat intelligence, vulnerability management programs, and vulnerability scanning.
HOW WE DELIVER
Our Team of
Expert Cybersecurity Consultants
Secutor has a team of over 100 Information Security and IT professionals working to provide the highest quality Threat & Vulnerability Management services possible for our customers. Secutor always puts people first, believing that when employees love working here, they’ll treat customers the same way.
- Only expert-level consultants, with an average of 23 years of industry experience
- Compliance expertise in COBIT, FFIEC, FISMA, HIPAA ISO 27001, NIST 800-37, PCI DSS, RMF and 800-53
Meet a Few of Our
Senior Team Members:

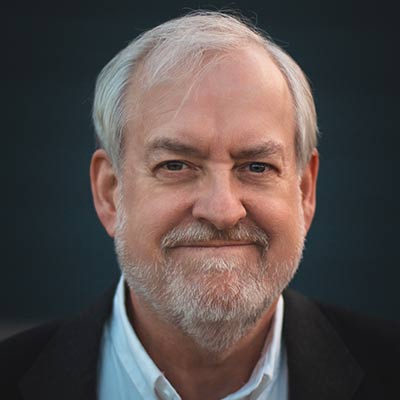
Kelly Hammons
CEO & VP of Customer Success

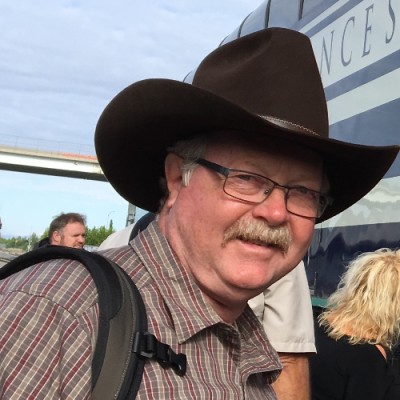
James Grisham
Chief Operations Officer & vCISO

Paul Mellen
IT Security Specialist

JP Hill
In Memoriam

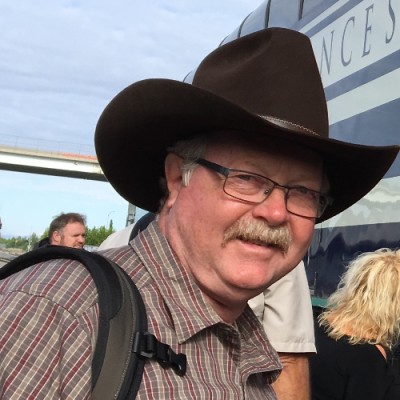
Mark Watjen
Implementation Consultant

Richard Eaton
CDPSE, Cisco SAEXS

Jennifer Bayuk
Cybersecurity Risk Management Expert

Andy Stokes
Senior Cyber Security Analyst
Jim Deerman
IT Security Consultant III

Brian Clinkenbeard
Expert Data Scientist

Paul Feather
Compliance Advisor

Leon Cook
Cybersecurity Leader
Meet a few of our
Senior Team Members

Kelly Hammons
CEO & VP of Customer Success
JP Hill
Virtual CISO, ISC2 Chapter President

Brian Clinkenbeard
Expert Data Scientist

Leon Cook
Cybersecurity Leader
Jim Deerman
IT Security Consultant III

Steve Blanding
CISO Consultant

Mark Watjen
Implementation Consultant

Richard Eaton
CDPSE, Cisco SAEXS
Join Our Team
A FEW OF OUR
Valued Partners
Secutor only uses the most reliable and trustworthy partners to provide services for our clients.
























WHY SECUTOR?
We Don't Just Sell Products. We Solve Problems.
Top
Talent
Top Cybersecurity Talent
People
First
People First
Proven
Methodologies
Proven Methodologies
Frequently Asked Questions
At the moment, we have over 115 expert consultants that we use to staff engagements.
Our consultants average over 23 years of experience in the industry. There is very little that we haven’t seen or dealt with in Information Security.
These devices have introduced many modern conveniences, but they’ve also made our jobs more challenging.
Now we must have some understanding of mobile device security, mobile device applications, Cloud security (many providers host their entire environments in the cloud).
The aforementioned social media applications have had the direct consequence of introducing new threat vectors and ways for cybercriminals to defraud the general public. Generally with phishing attacks.
The reason is that whenever new SQL injection vulnerabilities are found, Software Engineers react and go fix those specific problems. That means that they must write code, peer review it, perform regression testing (ie, make sure it doesn’t break existing functionality), quality assurance test it (make sure it fixes the problem), move the code into staging and then into production.
You can see why it is so important to catch a vulnerability in the early stages. But because most organizations don’t do much threat profiling, we tend to see a lot of issues caused either directly or indirectly by information technology processes like: server build and configuration processes, database implementation, application development, patching, disaster recovery, change management, and “desktop” support.
What Our Client's Say:
“